Cybersecurity Solutions, MSSP and ISO Compliance Tools
With 10+ years of experience as a Managed Security Service Provider, we deliver Virtual CISO services, ISO/IEC 27001:2022 and ISO/IEC 42001:2023 templates and guidance, cybersecurity tools, and CyberManager ISMS/AIMS software.










ISO Templates & Tools for Real Business Use
ISO 27001 and ISO 42001 Toolkits
ISO implementation should not begin with a blank page.
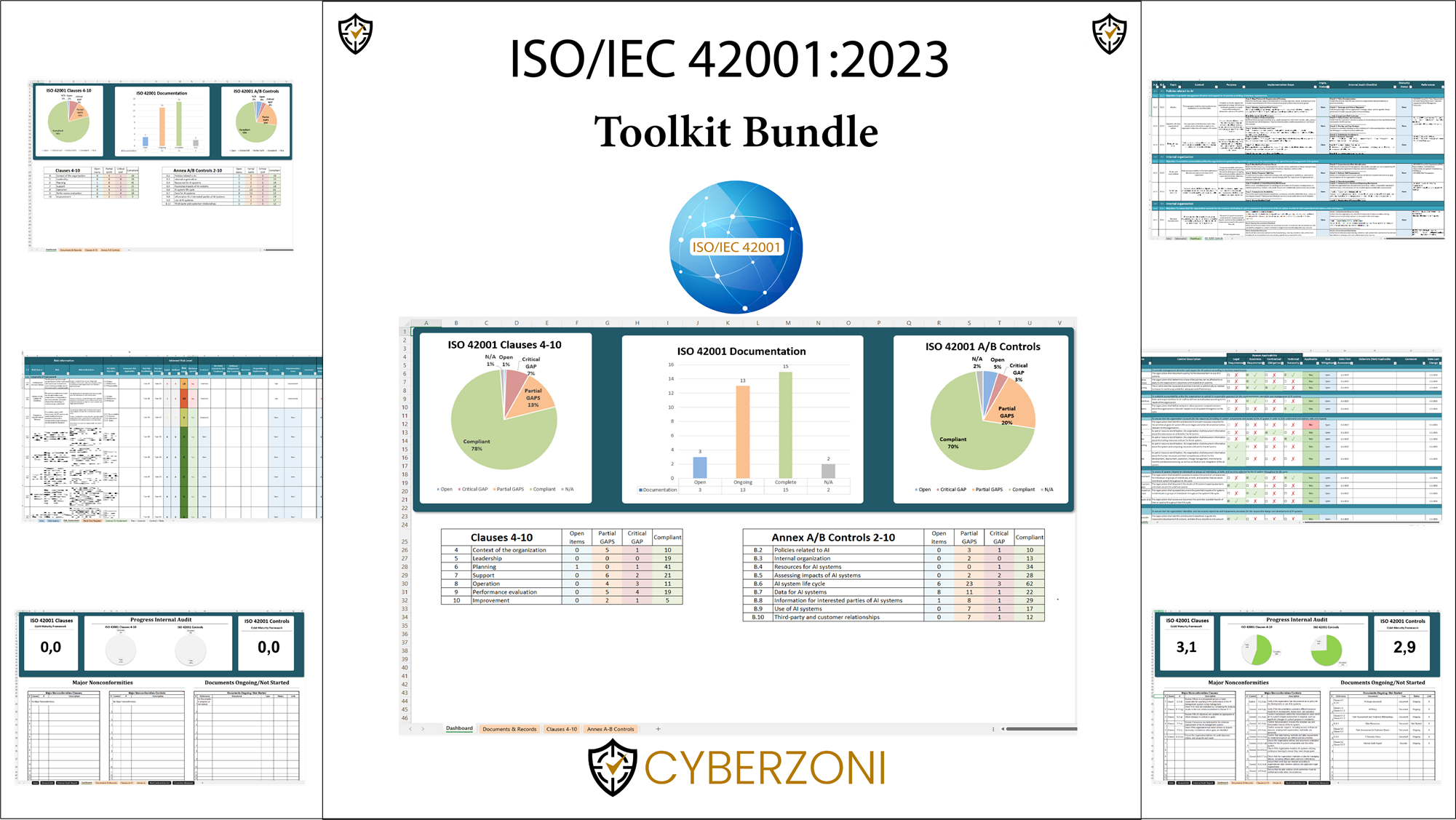
ISO 42001 Toolkit Bundle
✓ Configure your own ISO/IEC 42001 toolkit based on your organization’s needs.
✓ Structure AI governance, responsibilities, risks, controls and audit preparation.
✓ AIMS Templates, Policies, Procedures, Records
✓ Build a practical documentation foundation for your AIMS.
✓ Editable Word and Excel templates with instant download.
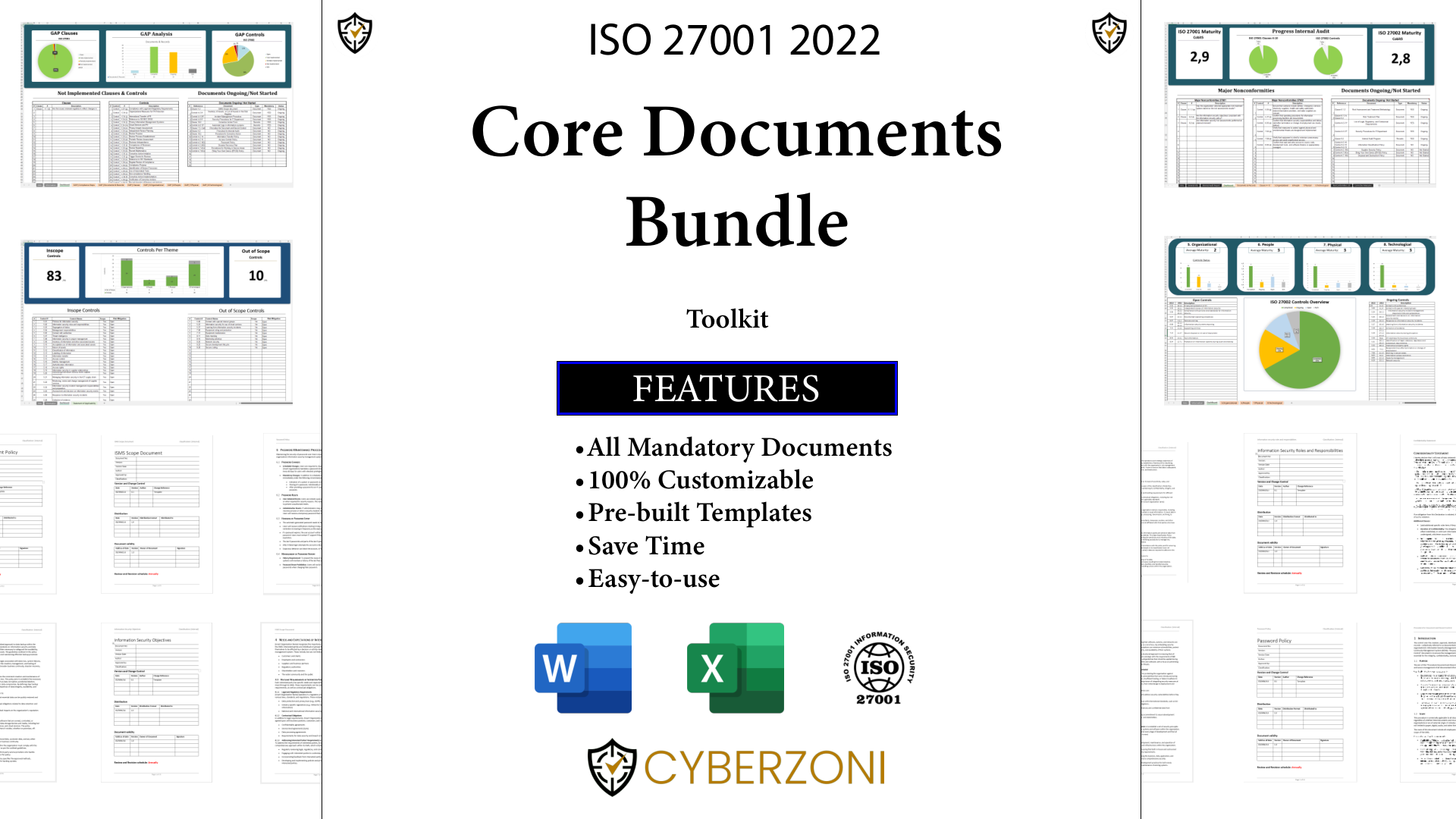
ISO 27001 Toolkit – Core Documents Bundle
Our ISO 27001 Toolkit draws on real business experience, helping organizations access practical ISMS documentation that can be applied directly in their compliance journey.
Latest ISO Templates & Tools
Discover the latest ISO document templates, checklists, and tools for faster compliance and audit preparation
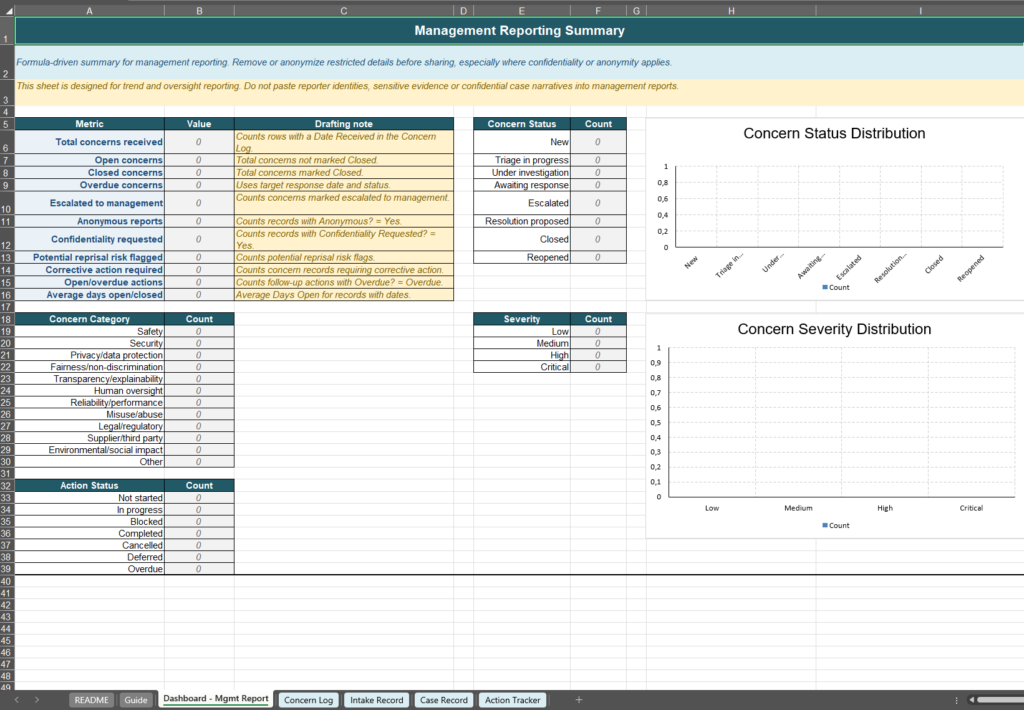
ISO 42001 Reporting of Concerns Records
✓ ISO 42001-aligned Reporting of Concerns Records
✓ Maintain a central register of AI-related concerns
✓ Complies with Annex A.3.3 & B.3.3
✓ Customizable Excel Template
✓ Instant Download
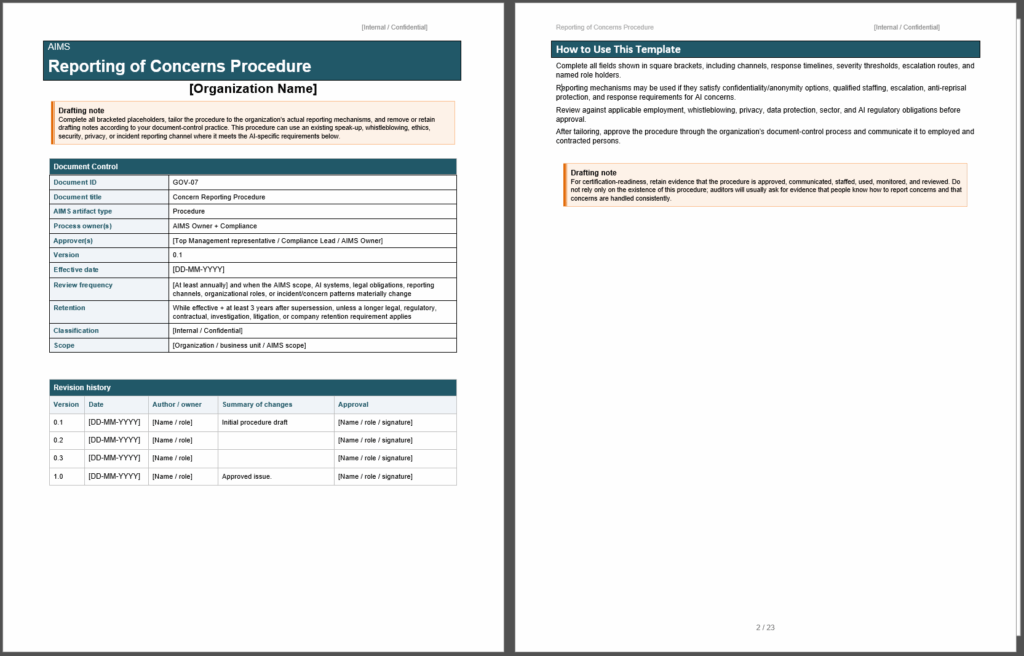
ISO 42001 Reporting of Concerns Procedure
✓ ISO 42001-aligned Reporting of Concerns Procedure
✓ AI Governance, Confidential Reporting, Escalation and Investigations
✓ Complies with Annex A.3.3 & B.3.3
✓ Customizable Word Template
✓ Instant Download
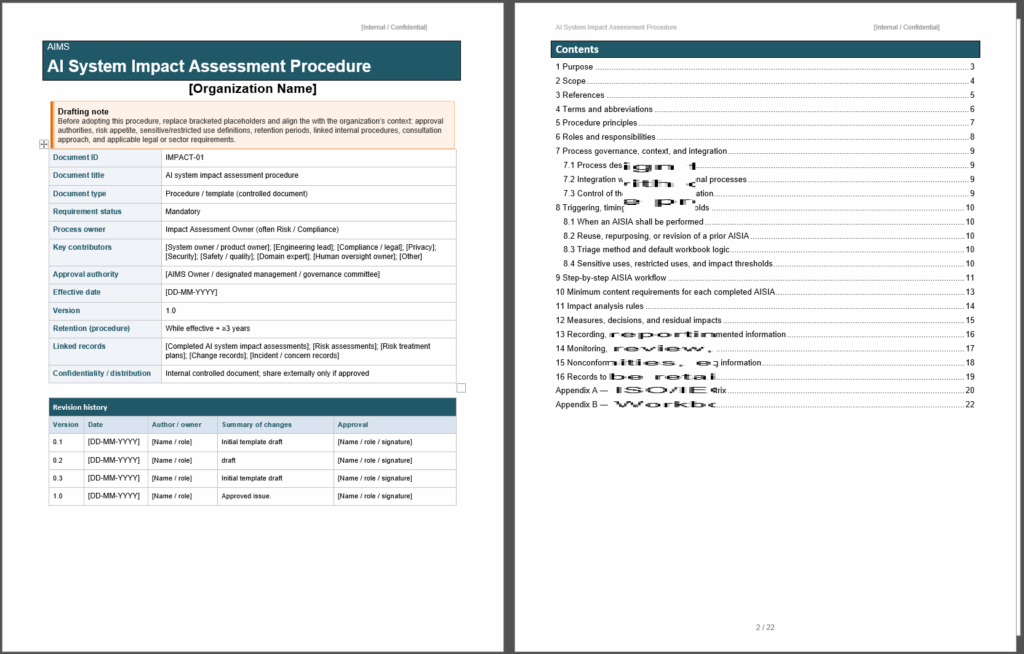
AI System Impact Assessment Procedure Template
✓ Editable AI System Impact Assessment Procedure Template
✓ ISO/IEC 42001 Clause 6.1.4 & 8.4 Compliance
✓ ISO/IEC 42001 Control A/B.5.2
✓ ISO/IEC 42005 aligned
✓ Instant Download
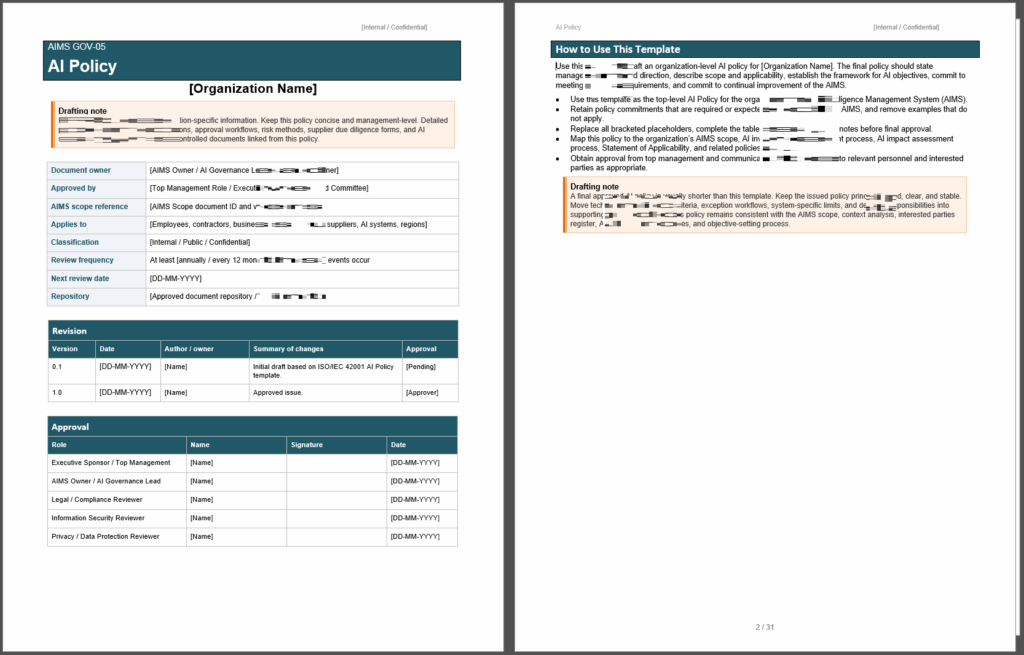
ISO 42001 AI Policy Template
✓ ISO/IEC 42001 AI Policy Template
✓ Document Top Management Commitments
✓ Clause 5.2 & A.2.2/B.2.2 Compliance
✓ Editable Word format
✓ Instant Download
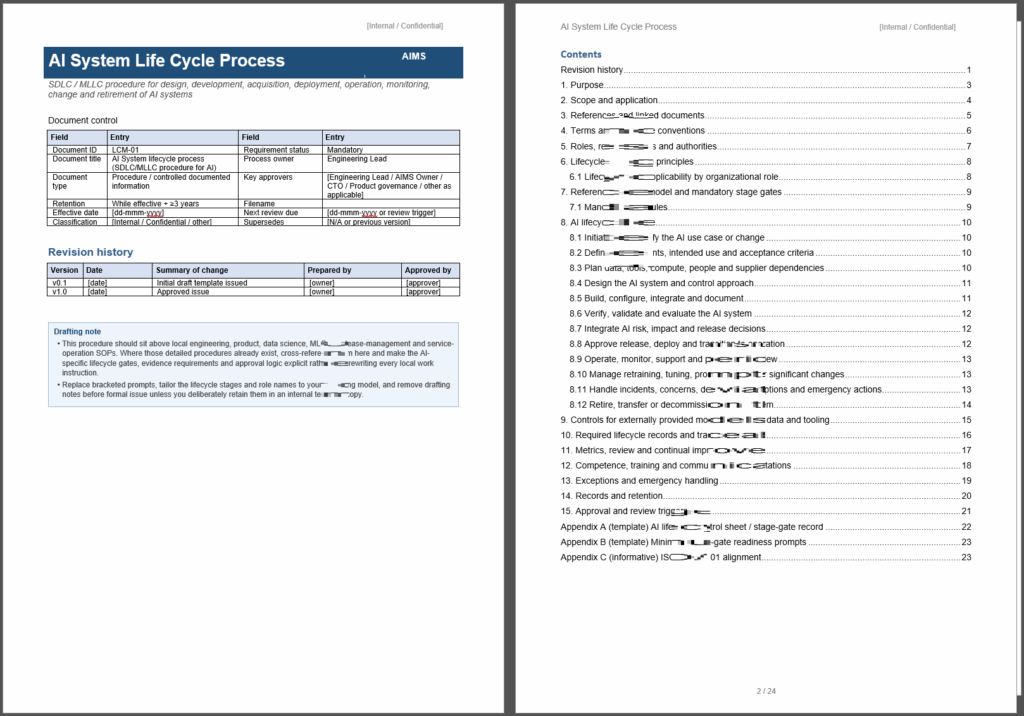
AI System Life Cycle Process Template
✓ AI System Life Cycle Procedure Template
✓ SDLC/MLLC for AI systems
✓ Alignment with ISO/IEC 42001
✓ Fully editable Word document
✓ Instant Download
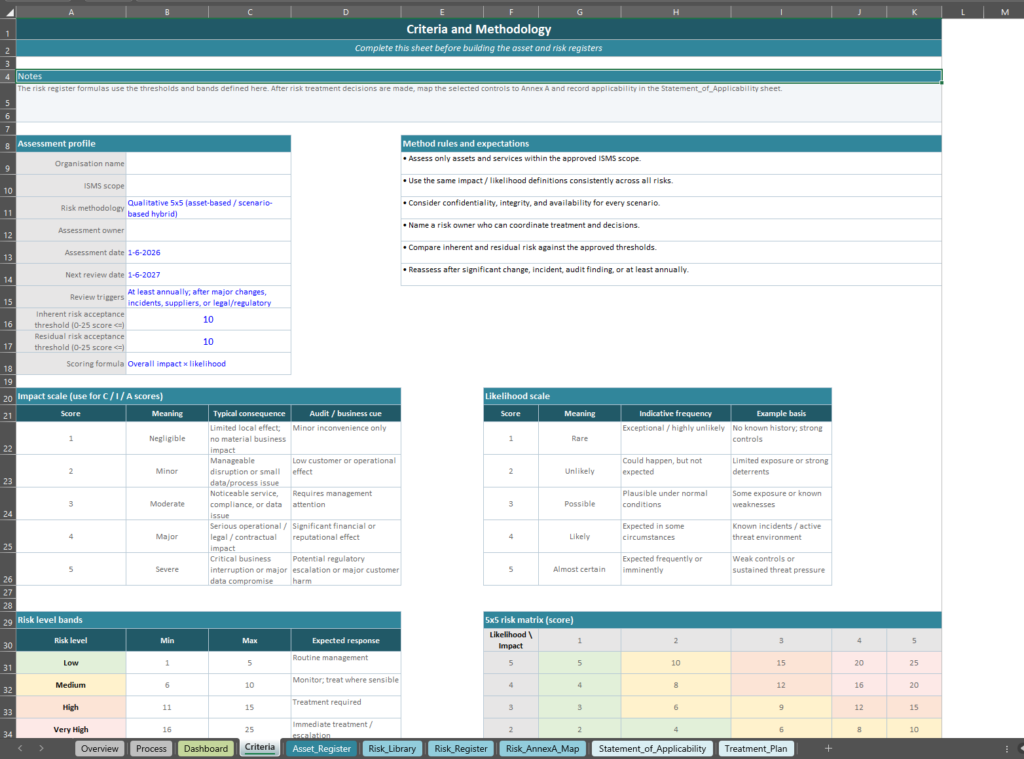
ISO 27001 Risk Assessment Template
✓ Excel-based ISO 27001 Risk Assessment Template
✓ Register Assets -> Register Risks -> Map Risks to Annex A Controls -> Treatment Plan
✓ Risks Library with Current Example Risks
✓ Address Clauses 6.1 – 8.2 – 8.3
✓ Instant Download
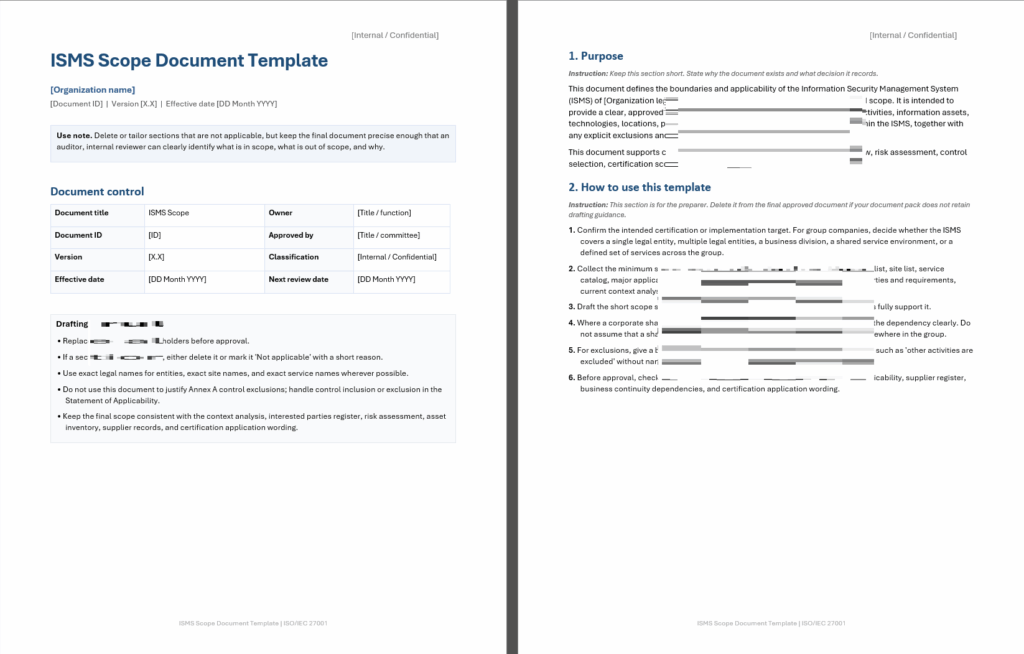
ISO 27001 ISMS Scope Document Template
This ISMS Scope Document Template gives you a strong starting point for documenting your ISMS Scope in compliance with ISO/IEC 27001 clause 4.3
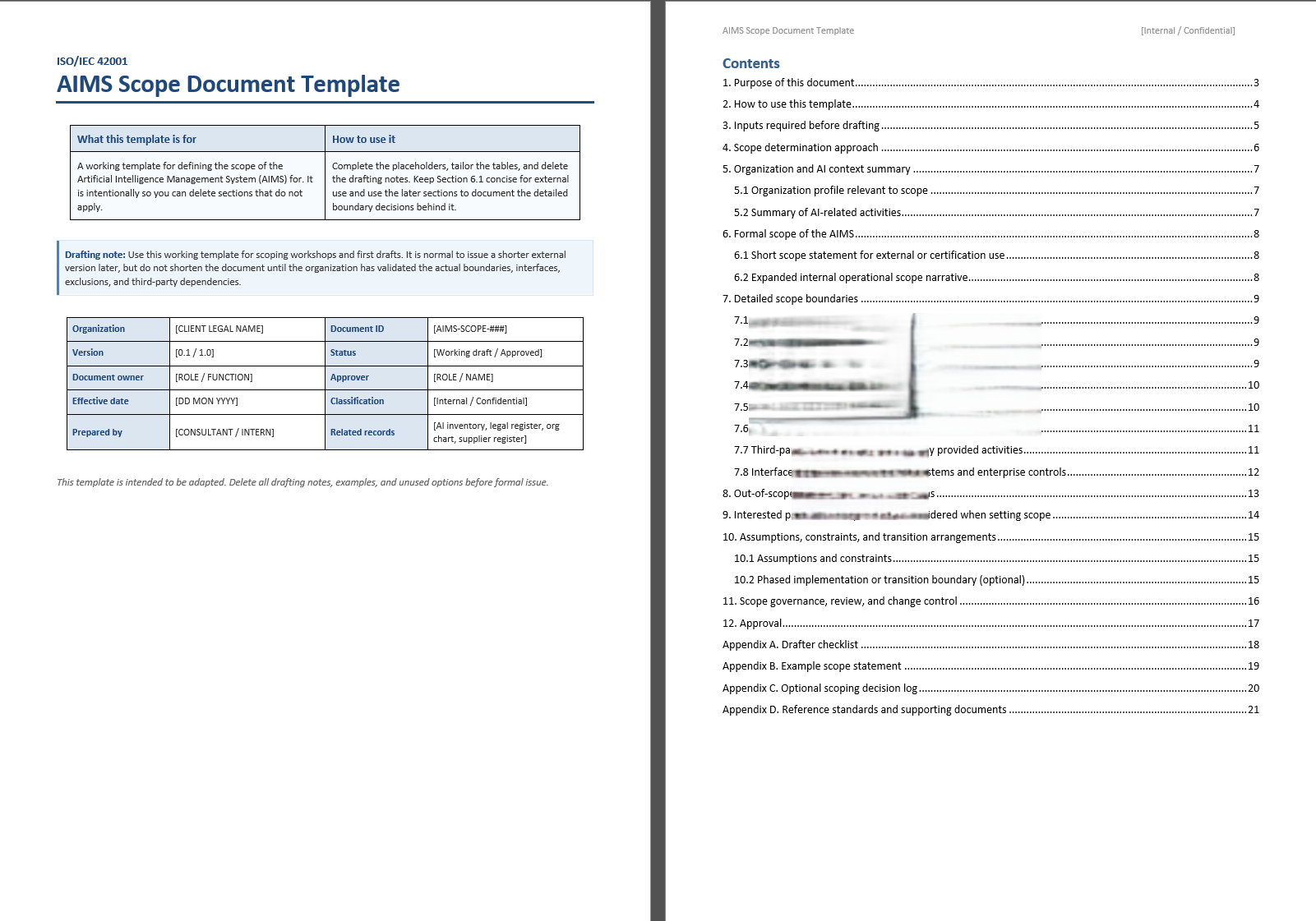
ISO 42001 AIMS Scope Document Template
✓ Determine AIMS Boundaries & Applicability
✓ ISO/IEC 42001 Clause 4.3 requirement
✓ Including Clause 4.1 & 4.2 Consideration
✓ Editable Scope Document Template
✓ Instant Download
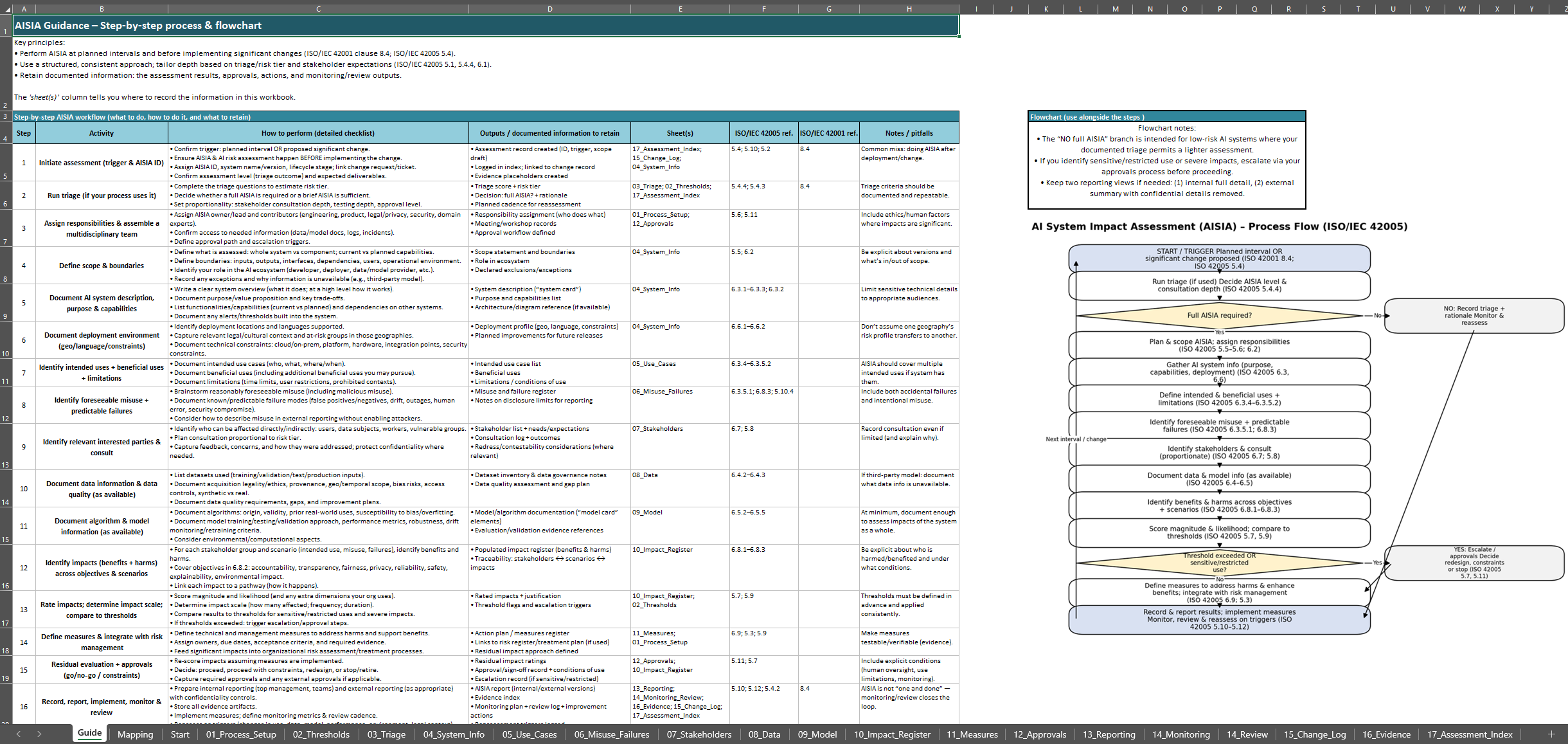
AI System Impact Assessment Template
✓ Editable Excel Template for AI System Impact Assessments
✓ Includes ISO/IEC 42005 Guidance
✓ ISO/IEC 42001 clause 8.4 Compliance
✓ With Free Email Support
✓ Instant Download
Protect Your Business with CyberZoni
We understand the importance of anticipating threats and vulnerabilities before they occur. That’s why we offer a wide range of proactive security solutions that help you stay ahead of potential dangers and protect your business from cyber attacks.
- Virtual CISO
- Enterprise-grade Cybersecurity Advice
- Control Design and Implementation
Managed CyberSecurity Services

We provide reliable and proactive Managed CyberSecurity Services to protect and advice your business from cyber risks.
Expertise and Specialization
Our team consists of industry leaders equipped with the latest knowledge on cyber threats and defensive technologies.
Cost Efficiency
We provide a cost-efficient solution by minimizing the expenses involved in staffing, training, and maintaining security operations
Industry-Specific Cybersecurity Expertise
Standard Compliance
Our services are designed to comply with standards like ISO/IEC:27001, ISO/IEC:42001, NIST SP 800-171, ISA/IEC:62443 and more.
- Industrial Control Systems Security
- Intellectual Property Protection
- Supply Chain Cybersecurity
- Manufacturing Industry Compliance
- IoT and Network Security
ABRO Compliance
We're uniquely equipped to address the specific needs of ABRO (Algemene Beveiligingseisen voor Rijksoverheidsopdrachten) compliance.
- Te Beschermen Belang (TBB) Strategies
- Cyber Beveiligings Functionaris (Cyber BF) Support
- ABRO 2026 Data Security Compliance
- ABRO 2026 Risk Management
- ABRO 2026 Monitoring and Reporting
Healthcare Compliance
Understanding the sector's distinctive challenges and compliance demands is at the forefront of our services, particularly our adherence to the NEN 7510 standard.
- NEN 7510 Compliance
- Electronic Health Records Security
- Medical Device Security
- Healthcare Data Privacy
- Healthcare Risk Management

Managed CyberSecurity
Stay a step ahead of cyber threats with our expert-managed services. Our custom approach covers all aspects of cybersecurity, protecting your data and applications. Gain cost-effective security and operational efficiency, letting you focus on business growth while we ensure your defenses are strong.
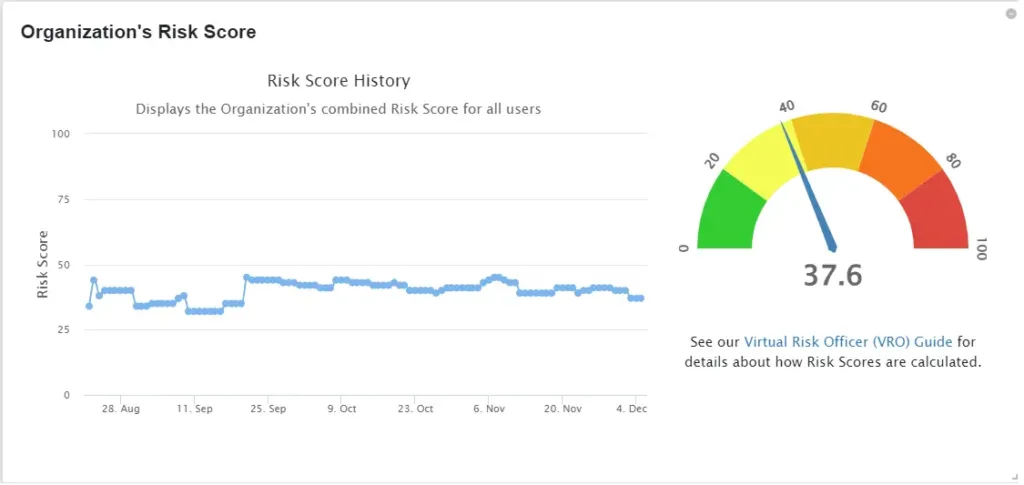
Pen-testing and vulnerability Scanning
Stay ahead of vulnerabilities with our Vulnerability Scanning service. Proactively detect and address potential security gaps, this service equips your business with the insights needed. Gain protection against threats, ensuring the safety and integrity of your data and systems.
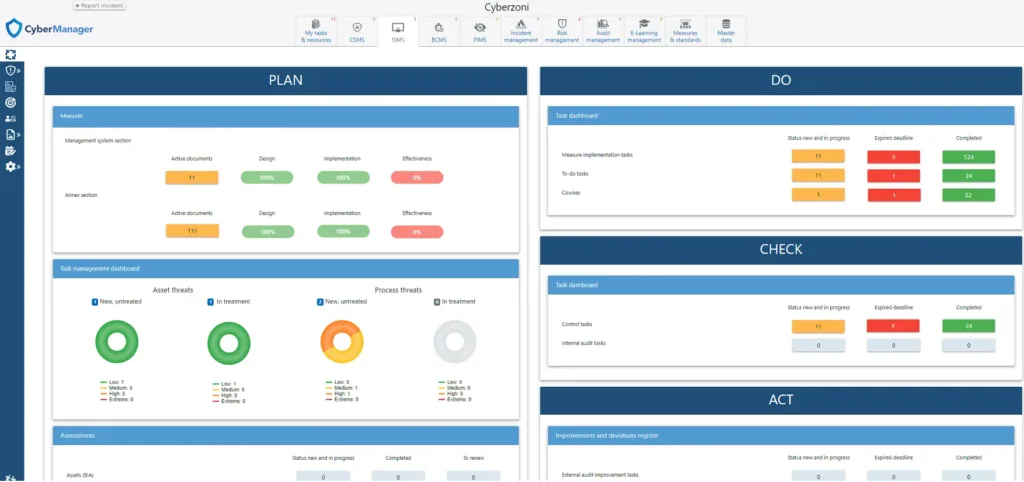
Cybermanager
CyberManager is your go-to solution for Information Security Management (ISMS). Simplify compliance, increase cybersecurity maturity, and reduce risks effectively. With CyberManager, you gain a powerful tool to manage information security.
Latest Articles
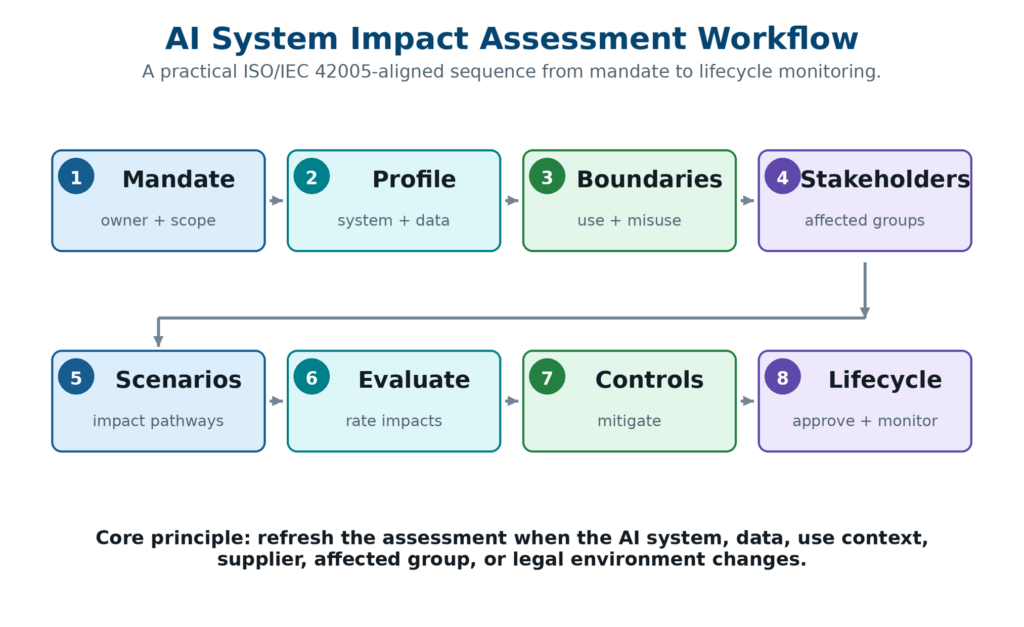
ISO/IEC 42005 AI System Impact Assessment | Step-by-Step
The guide walks through the full assessment lifecycle, from early concept screening and system profiling to impact scenario development, severity and likelihood analysis, control selection, residual impact evaluation, approval, monitoring, reassessment, and decommissioning.
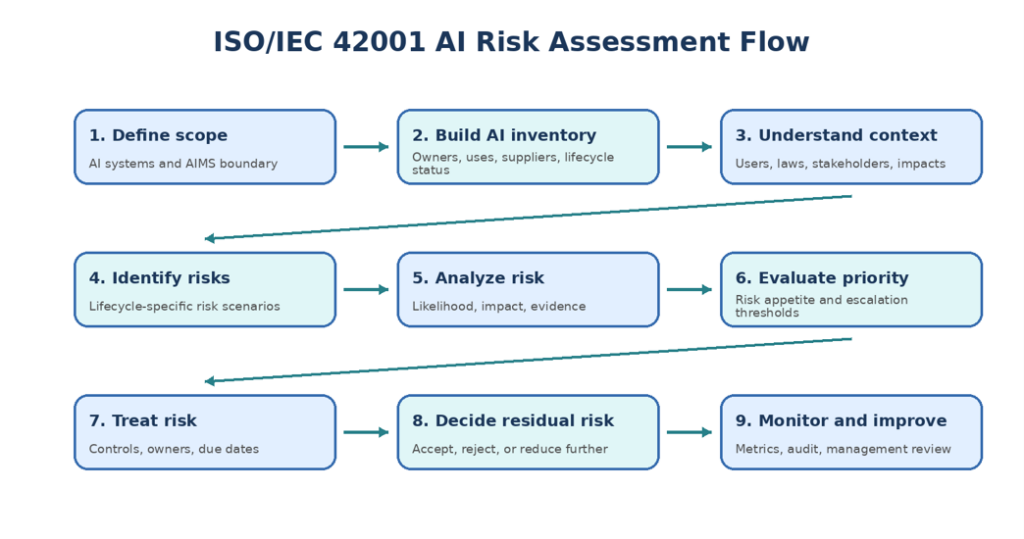
ISO/IEC 42001 AI Risk Assessment Step-by-Step Guide
A strong ISO/IEC 42001 AI risk assessment is a controlled management-system process that connects AI inventory, impact assessment, risk scoring, control selection, residual risk acceptance, monitoring, audit, and improvement.

Defining ISO 27001 templates and why organizations use them
ISO 27001 templates are pre-structured document and record formats—policies, procedures, registers, plans, forms, logs, and meeting-minute layouts—used to create and control the “documented information” that underpins an Information Security Management System (ISMS). They are not a substitute for an ISMS; they are accelerators and guardrails that help an organization produce coherent, auditable, and maintainable ISMS documentation aligned to the requirements of ISO/IEC 27001:2022.
What Our Clients Say About Us
The CISO support provided by CyberZoni was a game changer for our team. Their expert guidance on management and security awareness helped us secure our business from potential threats. I highly recommend them for startups looking to implement cybersecurity the right way!
Alex M.
Head of IT Security
We needed a more mature cybersecurity strategy that could scale as we grew. CyberZoni’s CISO Support was exactly what we needed. Their incident response planning and management advice made a huge difference.
Jennifer R.
Information Security Manager
After experiencing a data breach, we partnered with CyberZoni for full CISO support. Their hands-on approach to security management, from penetration testing to vendor security management, helped us a great deal.
Michael P.
Security Operations Manager